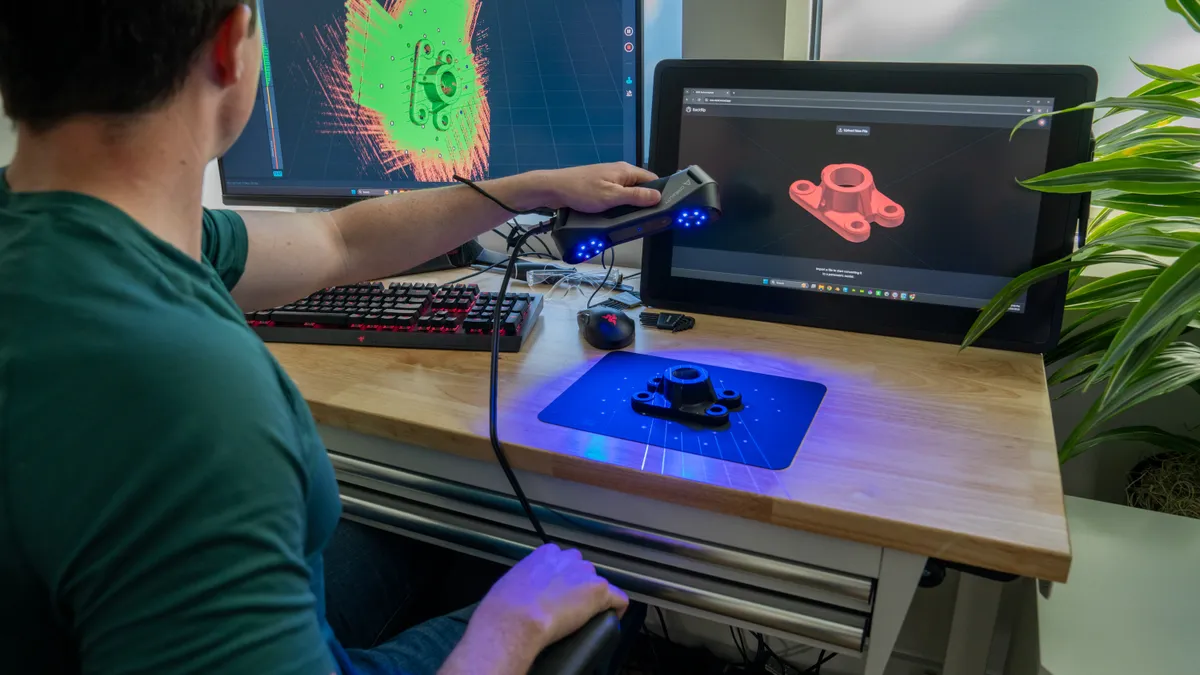
Manufacturers deploy 5G connectivity to take advantage of benefits such as the ability to connect to far more sensors, higher bandwidth, and cost reductions, but the combination of increased connectivity, antiquated legacy systems and lack of visibility has made manufacturing a lucrative target for adversaries.
In fact, manufacturing was the most targeted industry in 2022, with 447 compromised organizations publicly exposed on “leak sites,” according to the 2023 Unit 42 Ransomware and Extortion Report. (Unit 42 is Palo Alto Networks world-renowned threat intelligence and security consulting team.)
Weighing risks versus rewards
IT and OT managers must understand the risk landscape and carefully consider how they will leverage 5G to ensure they’re not inadvertently introducing security issues while enabling the business.
Benefits of 5G include:
- High speeds, low latency, and reliability: 5G networks offer higher data upload speeds compared to previous generations. They deliver extremely low latency, which means there’s minimal delay in data transmission. 5G networks are also designed for high reliability, with redundant connections and improved error correction. Industrial plants depend on this reliability to reduce downtime.
- Massive OT connectivity: 5G makes it easier to connect OT devices, allowing them to communicate with each other and with centralized systems for monitoring, control and data analysis. 5G's robust connectivity supports this massive device ecosystem, facilitating efficient data exchange across a broad array of interconnected assets. It's the backbone of the smart factories of the future, where machines work in harmony, transmitting real-time data to improve operational efficiency.
- Edge computing: 5G accelerates edge computing by keeping computing resources closer to the data source, which reduces latency and lets industrial companies process data locally. That improves response times for critical applications.
- Remote monitoring and control: With a transition to 5G, industrial companies have an opportunity to integrate security into their remote access practices.
Potential security risks include:
- Lack of visibility and security controls: Organizations are already struggling with the challenge of network and system visibility. Adding 5G to the mix exacerbates the issue, furthering the need for gaining comprehensive visibility as a foundation for creating a more secure environment.
- Increased attack surface: Adoption of 5G also adds to the attack surface, opening up more potential vectors for bad actors to access a network.
- More connected devices: 5G technologies enable greater capacity for billions of devices. Without reliable controls in place, that means more potential devices for bad actors to exploit and more devices that organizations need visibility into.
Mitigating the risk factors
Adopting a Zero Trust strategy can help manufacturing organizations overcome numerous security challenges associated with 5G. Additionally, it is crucial to tackle the supply chain risks in 5G networks, which may result from the deliberate or unintentional introduction of vulnerabilities. The arrival of 5G amplifies the potential attack surface, rendering each 5G network slice and virtual function vulnerable to targeted attacks. Mitigating this risk involves incorporating best practices such as isolation, segmentation, continuous logging, and filtering. It starts with gaining visibility, and the ability to identify all the devices on the network along with the associated risks for each. IT and OT leaders in manufacturing organizations can use a three-step approach to embracing Zero Trust:
- Identify what the organization needs to protect. Organizations must identify their most critical assets—their crown jewels—whose compromise would inflict the most severe operational damage. By recognizing and prioritizing these assets, organizations lay the foundation for targeted security.
- Apply least-privilege access. Assess what each asset connected to the network should have access to and decide what to allow – and nothing more. Then security teams can use behavioral analysis to flag any traffic that does not meet the organization’s definition of normal traffic. It’s the essence of Zero Trust: allow only the traffic that each user or system needs to do the job.
- Continuously monitor and validate. Access and traffic must be continuously monitored and continually validated to determine if access should be reduced or restricted based on the ongoing evaluation of risk. This includes understanding typical behavioral and traffic patterns to identify anomalous traffic that may indicate a compromise.
Zero Trust plus 5G: A more secure framework
By following these steps, organizations can effectively embrace the Zero Trust model to secure their 5G networks. While 5G introduces security challenges, the potential benefits it offers to manufacturers make the endeavor worthwhile. Properly secured and leveraged, 5G can transform industrial operations and productivity in unprecedented ways, ensuring a secure and efficient future for the manufacturing sector.